 To carry sensitive information, a system need be able to assure secrecy and privacy. A system cannot prevent unauthorized access to transmission media absolutely. Data tampering (an act of deliberately modifying the data through an unauthorised channel) is not a new issue, nor it is unique to computer era.
To carry sensitive information, a system need be able to assure secrecy and privacy. A system cannot prevent unauthorized access to transmission media absolutely. Data tampering (an act of deliberately modifying the data through an unauthorised channel) is not a new issue, nor it is unique to computer era.
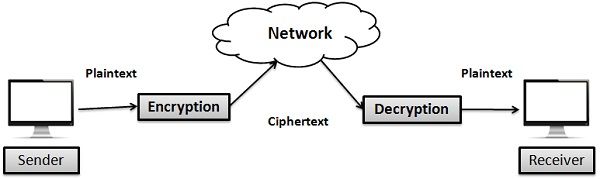
Altering the information could possibly protect it from unauthorised access, and as a result, the only authorised receiver can understand it. The method used in such a way is called encryption and decryption of information.
The major difference between Encryption and Decryption is that Encryption is the conversion of a message into an unintelligible form that is unreadable unless decrypted. While Decryption is the recovery of the original message from the encrypted data.
Content: Encryption Vs Decryption
Comparison Chart
| Basis for comparison | Encryption | Decryption |
|---|---|---|
| Basic | Conversion of a human understandable message into an unintelligible and obscure form that can not be interpreted. | Conversion of an unintelligible message into a comprehensible form which could be easily understood by a human. |
| Process takes place at | Sender's end | Receiver's end |
| Function | Conversion of plaintext into ciphertext. | Conversion of ciphertext into plaintext. |
Definition of Encryption
Encryption is the process in which a sender converts the original information to another form and sends the resulting unintelligible message out over the network. The sender requires an encryption algorithm and a key to transform the plaintext (original message) into a ciphertext (encrypted message), it’s also known as enciphering.
Plaintext is the data that need to be protected during transmission. The ciphertext is the scrambled text produced as an outcome of the encryption algorithm for which a specific key is used. The ciphertext is not shielded. It flows on the transmission channel. The encryption algorithm is a cryptographic algorithm that inputs plain text and an encryption key and produces a ciphertext.
In conventional encryption methods, the encryption and decryption keys are same and secret. Conventional methods are broadly divided into two classes: Character level encryption and Bit level Encryption.
- Character-level Encryption: In this method, encryption is performed at the character level. There are two common strategies for character-level encryption are substitutional and Transpositional.
- Bit- level Encryption: In this technique, firstly data (such as text, graphics, audio, video, etc.) is divided into blocks of bits, then modified by encoding/ decoding, permutation, substitution, exclusive OR, rotation, and so on.
Definition of Decryption
Decryption inverts the encryption process in order to convert the message back to its real form. The receiver uses a decryption algorithm and a key to transform the ciphertext back to original plaintext, it is also known as deciphering.
A mathematical process utilized for decryption that generates original plaintext as an outcome of any given ciphertext and decryption key is known as Decryption algorithm. This process is the reverse process of the encryption algorithm.
The keys used for encryption and decryption could be similar and dissimilar depending on the type of cryptosystems used (i.e., Symmetric key encryption and Asymmetric key encryption).
Key Differences Between Encryption and Decryption
- The encryption algorithm uses message (plaintext) and the key at the time of encryption process. On the other hand, in the process of decryption, the decryption algorithm converts the scrambled form of the message (i.e., ciphertext )with the help of a key.
- Encryption takes place at the sender’s end whereas decryption takes place at the receiver’s end.
- The major function of Encryption is to convert plaintext in the ciphertext. As against, decryption transforms ciphertext into plaintext.
Conclusion
The encryption and decryption processes fall under cryptology which is the combination of cryptography and cryptanalysis. Cryptography deals with the techniques for ensuring the security by encoding messages to make them non-readable. Cryptanalysis deals with the decoding of messages where an unintelligible form is converted back to intelligible form.
Encryption is used for enciphering the content at sender end before transmitting it over the network whereas decryption is used for deciphering the scrambled meaningless content at the receiver end.
Leave a Reply