 Digital Signature is an attachment to the electronic document which can be viewed as a signature. Once a document is signed, its data can not be altered without invalidating the signature. Digital Signature is created using signer’s key for encrypting the document.
Digital Signature is an attachment to the electronic document which can be viewed as a signature. Once a document is signed, its data can not be altered without invalidating the signature. Digital Signature is created using signer’s key for encrypting the document.
On the other side, Digital Certificate is a medium to prove holder’s identity for a particular electronic transaction. It grants certification to the people or website and also offers protection against data exchange from visitor to website.
The basic difference between Digital Signature and Digital Certificate is that there exists an association between a sender and the hosting site in Digital signature. Whereas in Digital Certificate, the holder doesn’t need to establish an association with the remote site. In fact, it just requires the ability to identify which digital certificate authority is used by the site to validate it.
Content: Digital Signature Vs Digital Certificate
Comparison Chart
| Basis for comparison | Digital Signature | Digital Certificate |
|---|---|---|
| Basic | It verifies the authenticity and source of a particular document. | It creates an identity of a website and also increases its trustworthiness. |
| Process | The document is encrypted at the sending end and decrypted at the receiving end using asymmetric keys. | A certificate is issued by a trusted agency known as CA which follow particular steps to do so that are - key generation, registration, verification and creation. |
| Security | It provides authentication, non-repudiation and integrity. | It provides authentication and security. |
Definition of Digital Signature
A digital signature is a technique that verifies the authenticity of the digital document in which particular code is attached to the message that acts as a signature. Hash of the message is utilized for the creation of the message and after that message is encrypted with the sender’s private key. The signature ensures the source and integrity of the message.
Techniques for digital signature
The Digital Signature Standard (DSS) was developed for performing the digital signature. The National Institute of Standards and Technology (NIST) issued the DSS standard as the Federal Information Processing Standard (FIPS) PUB 186 in 1991.
SHA-1 algorithm is used in DSS for computing the message digest against the original message and utilizes message digest to achieve digital signature. For doing so, DSS utilizes Digital signature algorithm (DSA). DSA is based on Asymmetric key cryptography.
Furthermore, RSA algorithm can also be used for performing digital signature, but its primary use is to encrypt the message. Although, DSA cannot be used for the encryption.
Definition of Digital Certificate
A Digital Certificate is simply a computer file which helps in establishing your identity. It officially approves the relation between the holder of the certificate (the user) and a particular public key. Thus, a digital certificate should include the user name and the user’s public key. This will prove that the certain public key owned by a particular user.
A digital certificate consists of the following information: Subject name (User’s name is referred to as Subject name because a digital certificate can be issued to an individual, a group or an organization), Serial number, Validity date range and issuer name, etc.
A Certification Authority (CA) is a trusted agency that can issue digital certificates to individuals and organizations, which want to use those certificates in the asymmetric key cryptographic application. Generally, a CA is a well-known organization, such as financial institution, post office, a software company, etc. The most popular CA’s are Verisign and Entrust.
CA accomplishes various tasks, for example, it issues new certificates, maintain old ones, and revoke the certificate that has become invalid for some sort of reasons, etc. The CA can delegate some of its tasks to this third-party called as a Registration Authority (RA).
Digital Certificate Creation Steps
- Key generation:It starts with the creation of the subject’s public and private keys using some software. This software works as a part of web browser and web server. The subject must not share the private key. The subject then sends the public key along with the other information like evidence about himself/herself to the RA (Registration Authority).
Although, either if the user has no knowledge about technicalities included in the creation of the key or if there are particular demands that the key must be centrally created then these keys can be created by RA also on the subject’s (user’s) behalf. - Registration: Suppose the user has created the key pair, the user now sends the public key and the related registration information (e.g. subject name, as it is needed to show in the digital certificate) and all the evidence of himself and herself to the RA.
For this, the software offers a wizard in which the user inserts the data and submits it when all the data is validated. Then the data moves over the network/internet to the RA. The format for the certificate requests has been standardized and is called certificate signing request (CSR). This is one of the public key cryptography standards (PKCS).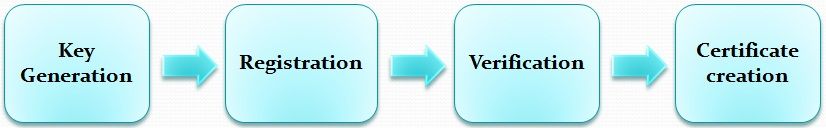
- Verification: When the registration process is completed, the RA has to check the user’s credentials such as the provided information is correct and acceptable or not. The second check is to ensure the user who is requesting for the certificate does indeed possess the private key correlating to the public key that is sent as the part of the certificate request to the RA. This inspection is called as checking the Proof Of Possession (POP) of the private key.
- Certificate creation: Suppose that all steps until now have been successfully executed, the RA accepts all the details of the user to the CA. The CA does its own verification (if required) and creates a digital certificate for the user.
There are programs for creating certificates in the X.509 standard format. The CA delivers the certificate to the user and also keep a copy of the certificate for its own record. The CA’s copy of the certificate is maintained in a certificate directory.
Key Differences Between Digital Signature and Digital Certificate
- The digital signature proves the authenticity of the digital document. On the other hand, digital certificate identifies the website.
- A digital certificate is digitally signed and can be used to sign other documents digitally. Digital signature of CA is verified on the digital certificate.
- Digital certificate creation process includes key generation, registration, verification and creation steps. In contrast, Digital signature process includes encryption and decryption of the message at the sender’s and receiver’s end respectively.
Conclusion
Digital Signature and Digital Certificate both are used for ensuring the authenticity of the digital document although these are absolutely different things. A document is digitally signed to protect it from tampering while Digital Certificate increases the trustworthiness of the website.
Ravi Sutrave says
excellent summary of these two terms. It clarified and even educates on both of these terms.. hats off to you for posting and sharing this.
Paula Williams says
The information you’ve shared in this blog is purely remarkable. Thanks for sharing.